Ashutosh Mallick
Posted on June 30, 2022

AWS Identity and Access Management (IAM)
What is IAM?
IAM stands for Identity and Access Management.
AWS Identity and Access Management (IAM) enables you to manage access to AWS services and resources securely.
IAM is a web services that enable you to manage users and group
permissions in AWSIAM gives you the flexibility to configure access based on your company’s specific operational and security needs.
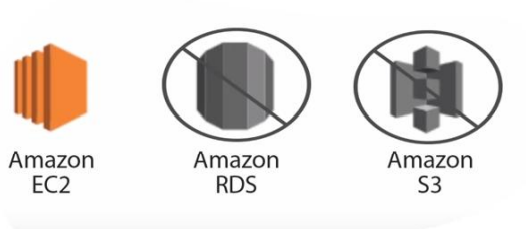
It is targeted at organizations with multiple users or systems that use AWS products such as Amazon Elastic Compute Cloud, Amazon Relational Database Service, and the AWS Management Console.
You do this by using a combination of IAM features, which are explored in detail in this lesson:
• IAM users, groups, and roles
• IAM policies
• Multi-factor authentication.
Why we go for IAM?
To avoid a security and logistical headache.
When you create an AWS account, it has permissions to do
anything and everything with all the resources.IAM Allows you to limit access as needed and gives you the
peace of mind that approved people are accessing the right
resources in the desired manner.IAM will allow us to create multiple users with individual security credentials and permissions, with this IAM, each user is allowed to do only what they need to do.
- Each user in the AWS account must have a unique set of credentials to access the console. Different types of users have different set of permission.
Developers need only access on Amazon Elastic Compute Cloud (EC2)
We can use IAM to create a unique user for each employee and define their permissions.
AWS Root user and IAM user
*AWS Account Root User *
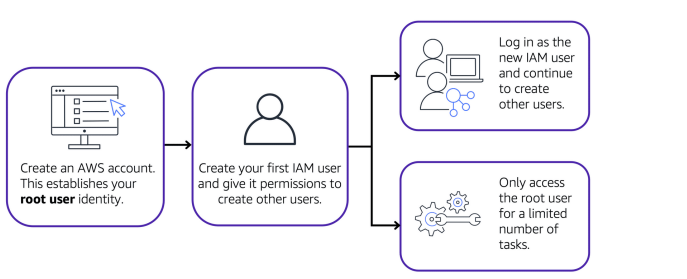
When you first create an AWS account, you begin with an identity known as the root user.
The root user is accessed by signing in with the email address and password that you used to create your AWS account.
You can think of the root user as being similar to the owner of the coffee shop. It has complete access to all the AWS services and resources in the account.
Best practices
Do not use the root user for everyday tasks. Instead, use the root user to create your first IAM user and assign it permissions to create other users.
Then, continue to create other IAM users, and access those identities for performing regular tasks throughout AWS.
Only use the root user when you need to perform a limited number of tasks that are only available to the root user.
Examples of these tasks include changing your root user email address and changing your AWS support plan.
IAM users
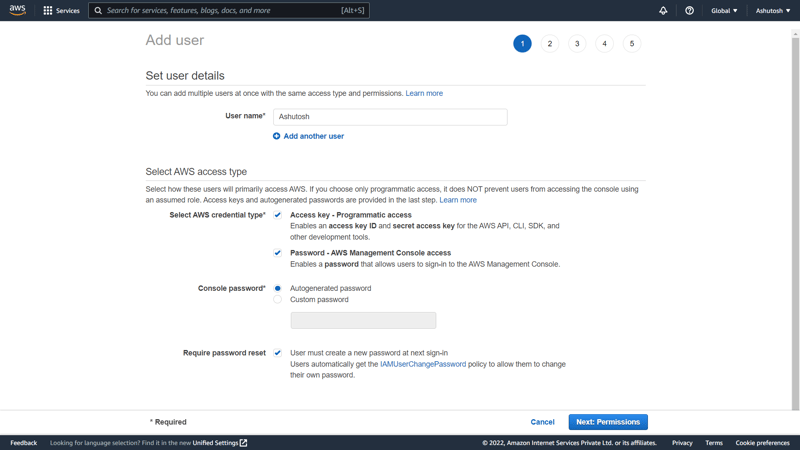
An IAM user is an identity that you create in AWS. It represents the person or application that interacts with AWS services and resources. It consists of a name and credentials.
By default, when you create a new IAM user in AWS, it has no permissions associated with it. To allow the IAM user to perform specific actions in AWS, such as launching an Amazon EC2 instance or creating an Amazon S3 bucket, you must grant the IAM user the necessary permissions.
Best practice:
- You should create individual IAM users for each person who needs to access AWS. Even if you have multiple employees who require the same level of access, you should create individual IAM users for each of them.
This provides additional security by allowing each IAM user to have a unique set of security credentials.
IAM policies
- An IAM policy is a document that allows or denies permissions to AWS services and resources.
- IAM policies enable you to customize users’ levels of access to resources. For example, you can allow users to access all of the Amazon S3 buckets within your AWS account, or only a specific bucket.
- By having IAM policies, you help to prevent users or roles from having more permissions than needed to perform their tasks.
- For example, if an employee needs access to only a specific bucket, specify the bucket in the IAM policy.
We do this instead of granting the employee access to all of the buckets in your AWS account.
Here’s an example of how IAM policies work. Suppose that the coffee shop owner has to create an IAM user for a newly hired cashier. The cashier needs access to the receipts kept in an Amazon S3 bucket
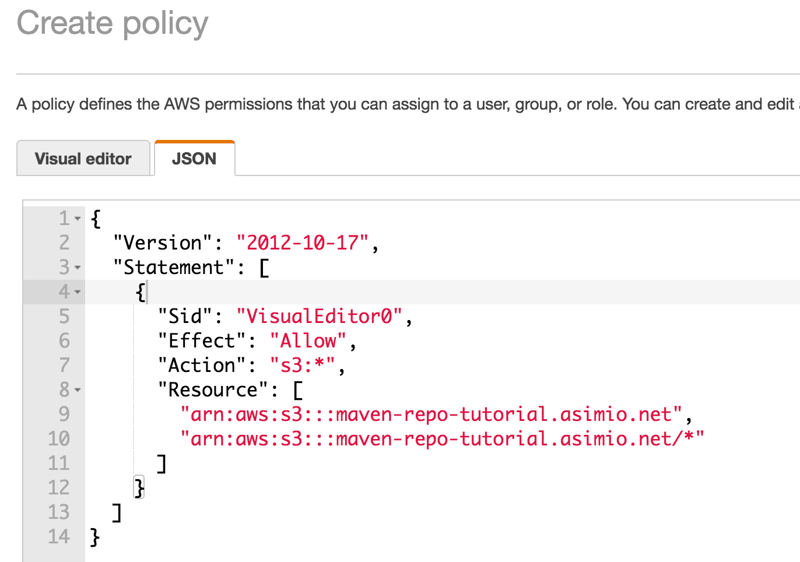
The below image represents an IAM policy writyten in json format.
In this example, the IAM policy is allowing a specific action within Amazon S3: ListObject. The policy also mentions a specific bucket ID: maven-repo-tutorial.asimi.net.
When the owner attaches this policy to the cashier’s IAM user, it will allow the cashier to view all of the objects in the maven-repo-tutorial.asimi.net bucket.
If the owner wants the cashier to be able to access other services and perform other actions in AWS, the owner must attach additional policies to specify these services and actions.
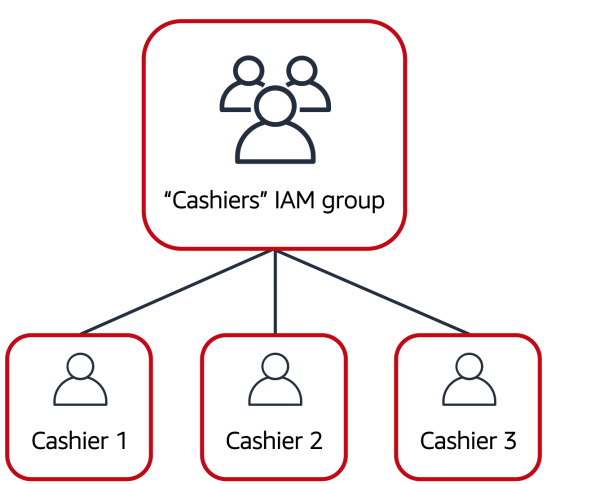
Now, suppose that the coffee shop has hired a few more cashiers. Instead of assigning permissions to each individual IAM user, the owner places the users into an IAM group.
IAM Groups
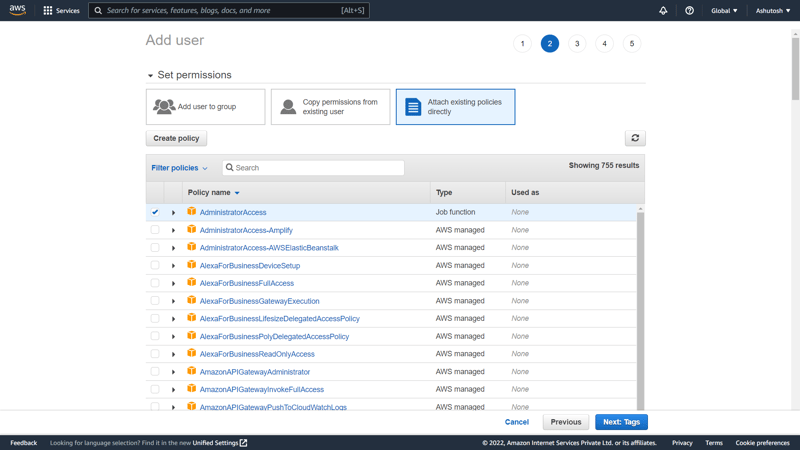
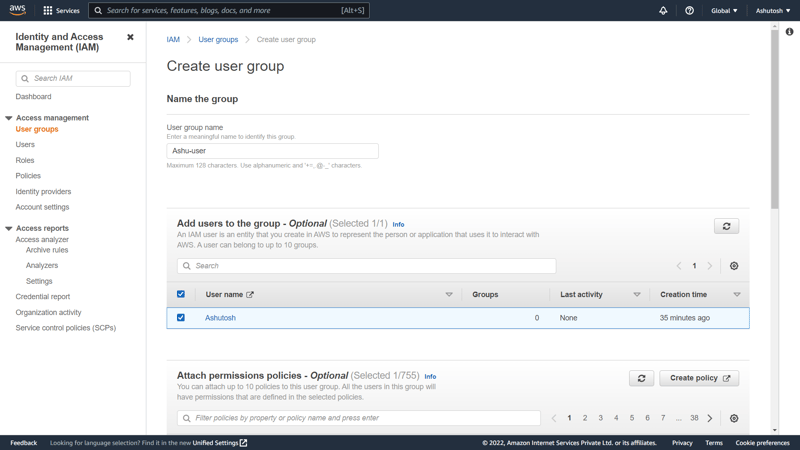
We can create IAM groups for smilar type of sevices like EC2 and S3. We can add custom policies for the group.
Policies will be applied to every user associated in the group, so we don't have to assign policies to each user manually.
An IAM group is a collection of IAM users. When you assign an IAM policy to a group, all users in the group are granted permissions specified by the policy.
Here’s an example of how this might work in the coffee shop. Instead of assigning permissions to cashiers one at a time, the owner can create a “Cashiers” IAM group. The owner can then add IAM users to the group and then attach permissions at the group level.
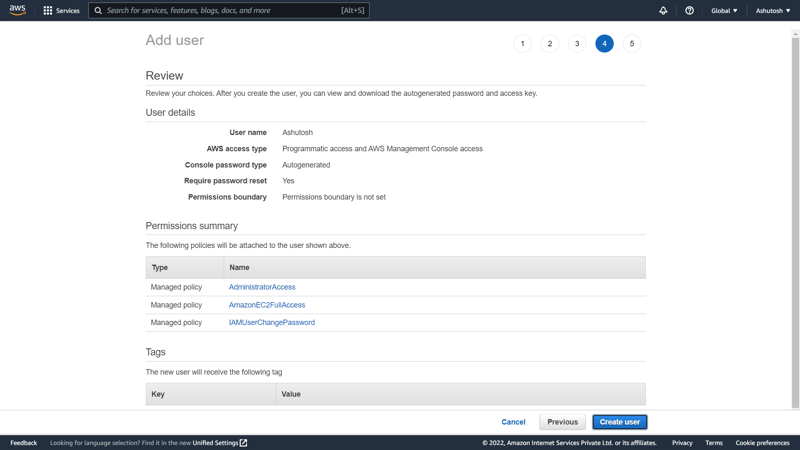
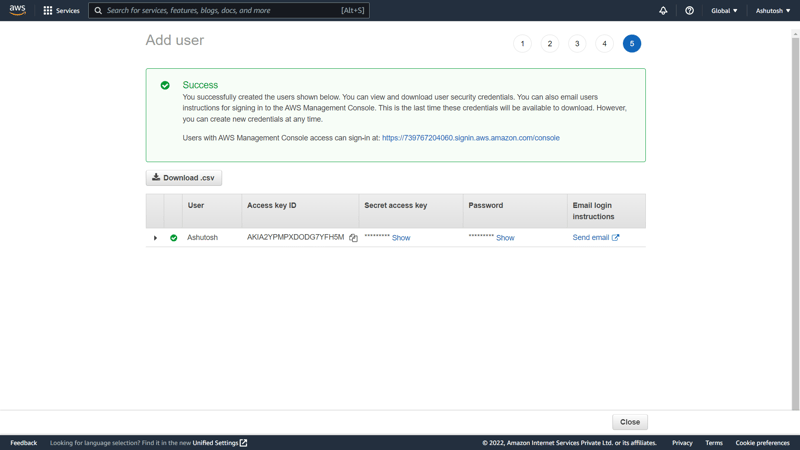
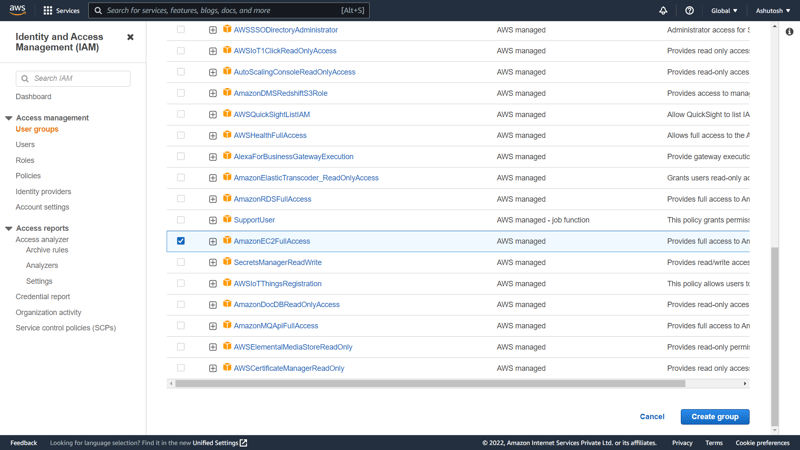
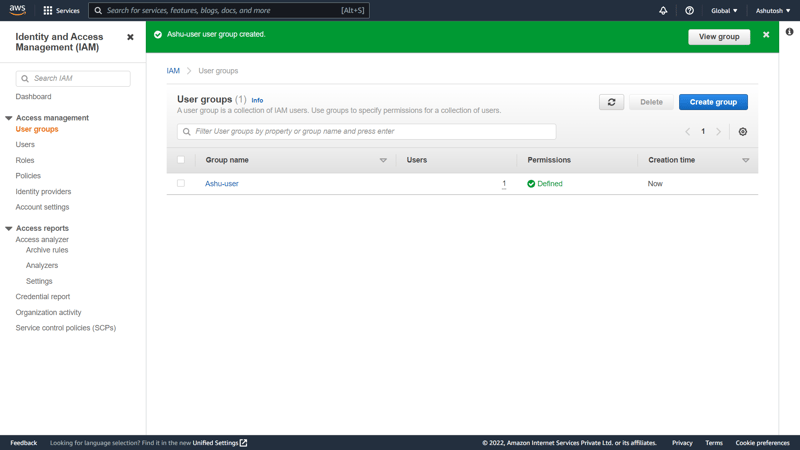
Below pictures include the creation process of an IAM user group in AWS console.
- Assigning IAM policies at the group level also makes it easier to adjust permissions when an employee transfers to a different job.
- For example, if a cashier becomes an inventory specialist, the coffee shop owner removes them from the “Cashiers” IAM group and adds them into the “Inventory Specialists” IAM group. This ensures that employees have only the permissions that are required for their current role.
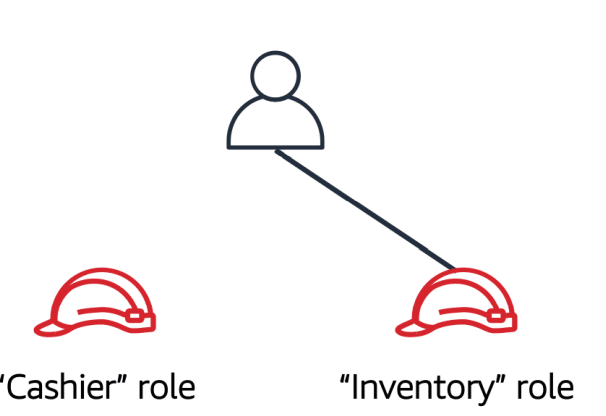
IAM Roles
Using IAM roles we can attach S3 and EC2 with each other(kind of pipelining), in this case we don't have to use ID and Password.
An IAM role is an identity that you can assume to gain temporary access to permissions.
Before an IAM user, application, or service can assume an IAM role, they must be granted permissions to switch to the role.
When someone assumes an IAM role, they abandon all previous permissions that they had under a previous role and assume the permissions of the new role.
IAM roles are ideal for situations in which access to services or resources needs to be granted temporarily, instead of long-term.
Example of IAM Roles
An example of how IAM roles could be used in the coffee shop:
First, the owner grants the employee permissions to switch to a role for each workstation in the coffee shop.
Next, the employee begins their day by assuming the “Cashier” role. This grants them access to the cash register system.
Later in the day, the employee needs to update the inventory system. They assume the “Inventory” role. This grants the employee access to the inventory system and also revokes their access to the cash register system.
Multi-factor Authentication
When you sign in to Gmail(say) it requires you to provide multiple pieces of information to verify your identity. Such as you might have needed to provide your password and then a second form of authentication, such as a random code sent to your phone.
This is an example of multi-factor authentication. In IAM, multi-factor authentication (MFA) provides an extra layer of security for your AWS account. This is also called as Hardening of AWS account.
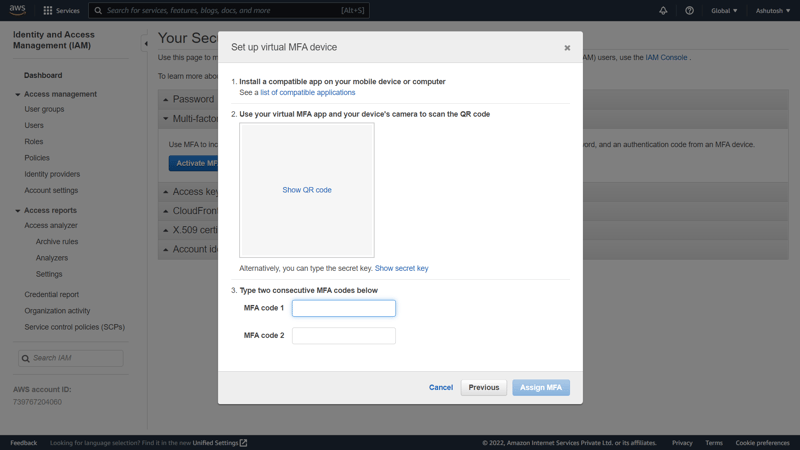
Setup:
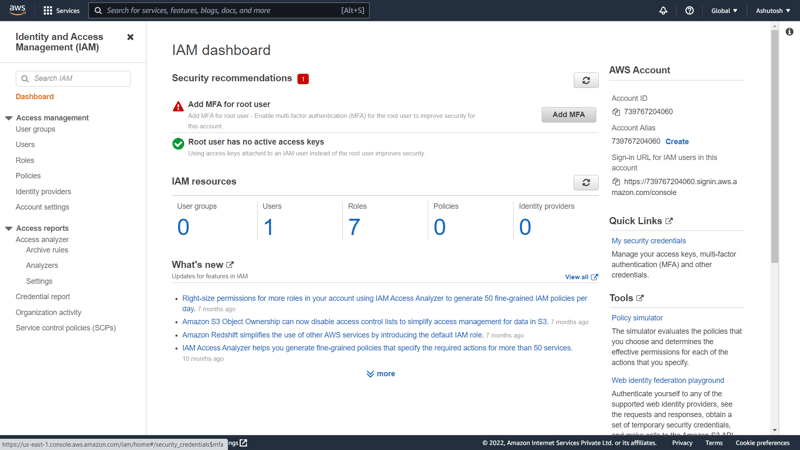
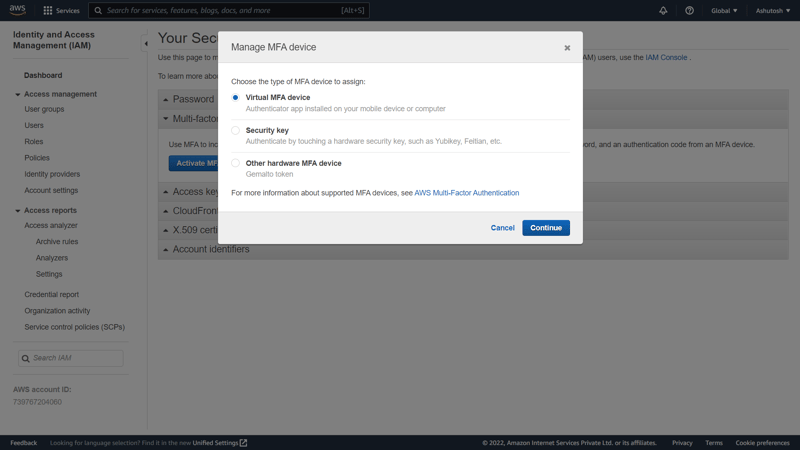
- ON IAM dashboard click on activate MFA.
- Then click on virtual MFA device. We use an authenticator app in our cell phone as MFA device to scan the QR code and to activate MFA.
- After scanning the QR code via authenticator app we get MAF1 and MFA2 codes.
- On next login for every user they'll have to undergo MFA authentication.
- We can also activate MFA via AWS CLI. But we have to provide access key and secret key in this case. So it's better not to go ahead with this step as anyone can access our ervices if they get the keys.
Thank you !!
Follow me for more detailed contents on AWS services :)

Posted on June 30, 2022
Join Our Newsletter. No Spam, Only the good stuff.
Sign up to receive the latest update from our blog.
Related
October 29, 2024